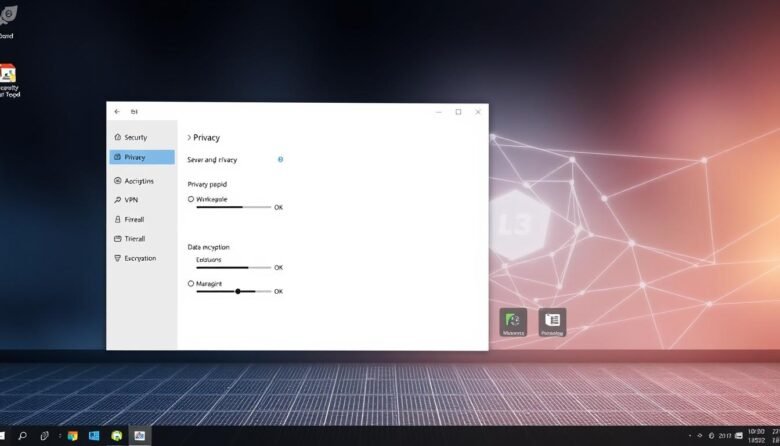
This short guide walks U.S. users through the best built‑in privacy choices for a cleaner, safer PC experience. You’ll get a friendly, practical tour of account and identity controls, on‑device encryption, and browser settings that limit what your system shares by default. We show step‑by‑step ways to harden a new or existing machine without buying …
Your last line of defense for critical files is a clear, practical plan you can trust. World Backup Day has evolved into Cyber Protection Week, and that shift shows why resilient storage and recovery matter now more than ever. This short guide is for readers in the United States who want a friendly path to …
Nearly one in four people have faced fraud, so spotting threats matters. This guide shows simple checks you can use every day to verify information and reduce risk. Modern technology helps a lot: search filters, browser protections, and on-device models block many fraudulent pages and calls before you interact. You’ll get a step-by-step workflow to …
Cookies are small files that websites place on your device to keep you signed in, remember preferences, and deliver local content. Clearing those files can sign you out and delete saved settings, but it also helps protect your privacy and reduce profiling across sites. This guide walks you step-by-step through major browsers so you can …
Keeping your online profiles private helps protect you from burglars, stalkers, and fraud. Start by reviewing each service and its controls so you know what others can see. Remember: “private” usually limits people, not the company behind a platform. Use strong, unique passwords and enable two-factor authentication on every account. Audit any connected apps that …
Everyday users and small businesses face a real digital threat that can lock or steal their data. Modern attacks move in stages, so there are many chances to stop an incident before it harms your files. This short guide explains how attackers gain access, how they hide and spread, and what practical steps you can …
Modern life means dozens — even hundreds — of logins to remember. Studies show nearly 35% of people reuse the same credential for most sites, and 42% say they have had an account hacked. With the average person using more than 200 accounts, manual creation and recall of unique codes is unrealistic. A password manager …
Modern email protection blends technology, policy, and people to keep messages safe without slowing your business. In simple terms, this framework defends the confidentiality, integrity, and availability of communications by using layered tools like signatures, machine learning, and behavioral analytics. Proofpoint found nearly every organization faced account takeover attempts in 2024, and millions of BEC …
This friendly guide shows simple, high-impact ways to protect your personal details and reduce the chance of fraud. You’ll learn everyday habits that save time and stress, from guarding Social Security data to spotting phishing attempts. Start with small changes: use stronger passwords, turn on multifactor authentication, and share less information publicly. Secure your devices …
Protect your data while you send documents and photos across the U.S. This service combines end-to-end encryption with simple controls so sensitive content never leaks to unintended people. The interface keeps daily actions familiar: pick recipients, set permissions, and email a link. Gmail uploads items over 25 MB to cloud storage and inserts a safe …